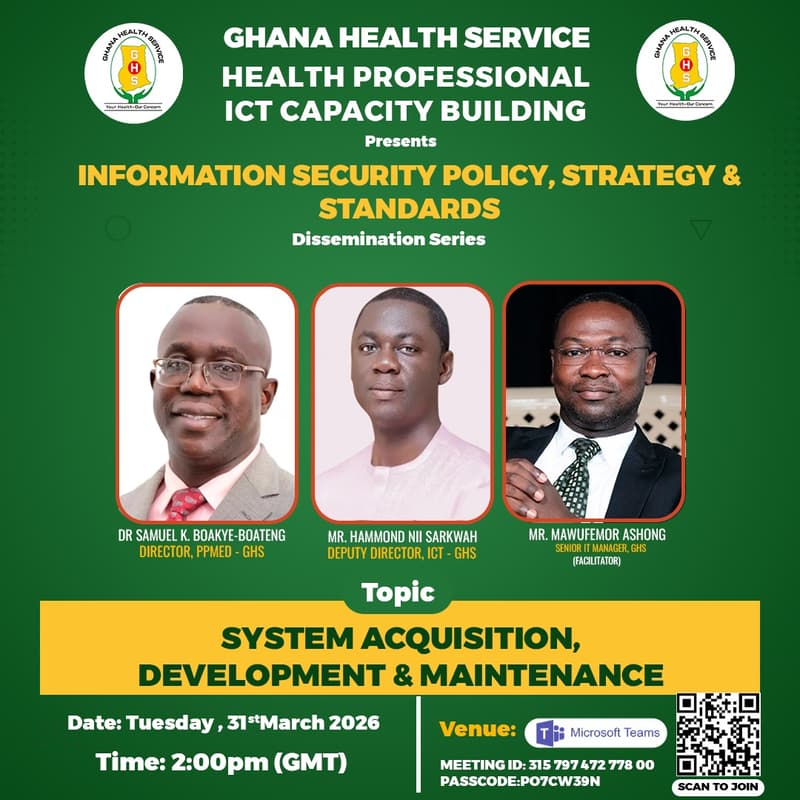
System Acquisition, Development and Maintenance
Information Security plays a critical role in the health sector due to the volume and sensitivity of data used in healthcare delivery. The Health Sector has been designated as a Critical Information Infrastructure (CII) by the Cyber Security Authority (CSA), meaning any disruption to its digital systems could significantly affect national security and public wellbeing.
As a public health institution, the Ghana Health Service (GHS) is responsible for safeguarding Protected Health Information (PHI) and ensuring the confidentiality, integrity, and availability of its digital systems and data. To support this responsibility, GHS has developed and is implementing an Information Security Policy, Strategy, and Standards to guide and protect its ICT ecosystem.
This session focuses on System Acquisition, Development and Maintenance (Section 4.20), which establishes security requirements for the procurement, development, deployment, and management of ICT systems within GHS.
Purpose of the Webinar
This webinar is part of the ongoing dissemination of the GHS Information Security Policies and focuses on System Acquisition, Development and Maintenance (Section 4.20).
It aims to improve staff understanding of the security and governance requirements guiding how ICT systems are procured, developed, implemented, and maintained within the Service.
Webinar Objective
The objective of this webinar is to strengthen staff capacity to implement the System Acquisition, Development and Maintenance Policy by ensuring that all ICT systems used within GHS comply with procurement regulations, security best practices, and approved ICT governance structures.
Presentation Highlights
Overview of System Acquisition, Development and Maintenance (Section 4.20) within the GHS Information Security Policy.
ICT System Procurement
Requirements for acquiring ICT systems within GHS.
Role of the Head of ICT in reviewing technology acquisitions.
Security review and acceptance testing for purchased or donated systems.
Software Licensing and Compliance
Proper use of open-source and licensed software.
Importance of valid software licensing agreements.
System Implementation
Safe transition from old systems to new systems through parallel implementation.
Outsourced and Cloud Services
Use of cloud services such as SaaS, IaaS, and PaaS.
Agreements and security requirements for third-party service providers.
In-House System Development
Ownership of systems developed by GHS staff.
Confidentiality and protection of system source code.
Secure Development and Testing
Separation of development, testing, and live environments to reduce risk.
Mobile Devices and BYOD Security
Security requirements for staff using mobile or personal devices for work.
Device protection, updates, anti-malware, and access restrictions.
Policy Compliance
Use of authorized devices only.
Adherence to procurement and ICT governance regulations.
Live Demonstration
A live practical demonstration will be conducted
For more inquiries, call Benjamin +233 24 124 6642