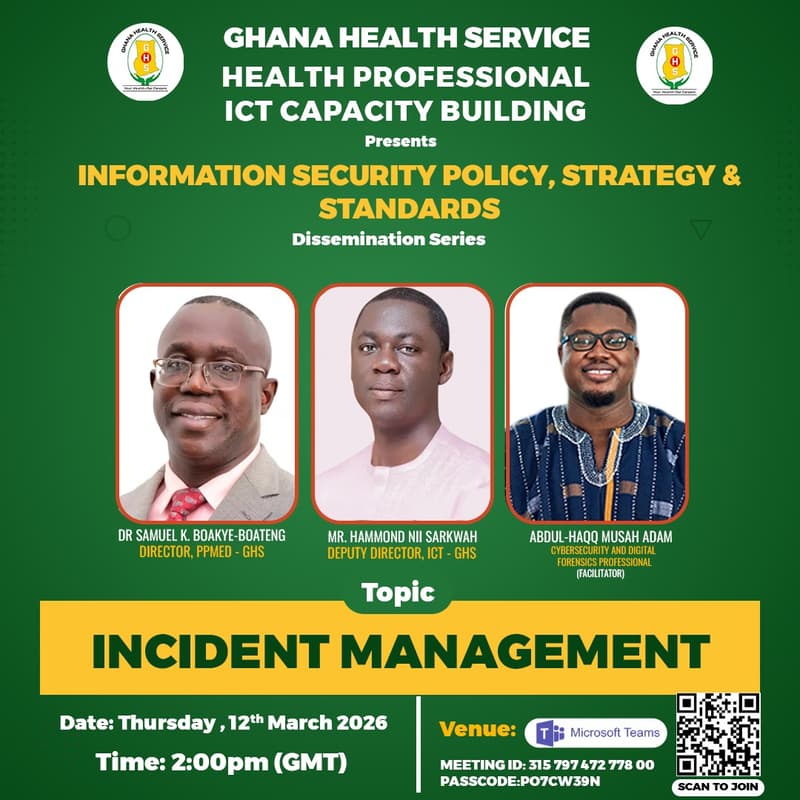
Incident Management
Information Security plays a critical role in the health sector due to the volume and sensitivity of data routinely handled in the delivery of healthcare services. The Health Sector has been designated as a Critical Information Infrastructure (CII) by the Cyber Security Authority (CSA), as any disruption to its systems, networks, processes, or information assets could have a devastating impact on national security and the social and economic well-being of the population.
As a public health institution, the Ghana Health Service (GHS) is responsible for safeguarding Protected Health Information (PHI) and ensuring the confidentiality, integrity, and availability of its digital systems and data. In response to this responsibility, GHS has developed and is implementing an Information Security Policy, Strategy, and Standards to guide, direct, and protect its ICT ecosystem.
These policies apply to all digital assets of the Service and are binding on all staff and third-party service providers. They are designed to proactively identify and mitigate risks that could compromise system availability, data integrity, confidentiality, service delivery, and the Service's reputation.
Purpose of the Webinar
This webinar forms part of the ongoing dissemination of the Ghana Health Service (GHS) Information Security Policies and focuses specifically on Incident Management (Section 4.19). It aims to strengthen understanding of how GHS identifies, reports, responds to, and manages cybersecurity incidents that may affect patient care, privacy, safety, and service continuity.
Webinar Objective
The objective of this webinar is to strengthen staff capacity within the Ghana Health Service to effectively implement the Incident Management Policy by ensuring timely identification, reporting, containment, and response to cybersecurity incidents, while maintaining regulatory compliance with the Cyber Security Authority and supporting collaboration with the National Computer Emergency Response Team - Ghana (CERT-GH) to safeguard patient care, privacy, and business continuity.
Presentation Highlights
Overview of Incident Management within the GHS Information Security Policy (Section 4.19).
Understanding cybersecurity incidents in healthcare and their impact on patient care and privacy.
Regulatory compliance requirements and reporting obligations to the Cyber Security Authority (CSA).
Structured Incident Response methodologies:
Lockheed Martin Kill Chain Principle
Diamond Model of Intrusion
Immediate reporting procedures to the Head of ICT for all incidents and suspected system flaws.
Role and structure of the Computer Security Incident Response Team (CSIRT).
Collaboration framework between GHS CSIRT and CERT-GH.
Incident containment, eradication, recovery, and post-incident review processes.
Business continuity expectations and acceptable downtime thresholds.
Staff roles and responsibilities in supporting rapid detection, escalation, and response.
Live Demonstration
A live practical demonstration will be conducted
For more inquiries, call Benjamin +233 24 124 6642